Benefits Of Focusing On Software Supply Chain Security
Open source is now everywhere! The question for businesses isn’t whether or not they use open-source code. It’s about how much and what kind of open source code you use.
If you don’t know what’s in your software supply chain, an upstream vulnerability in one of your dependencies can affect your application, making you vulnerable to a possible compromise.
In this article, we’ll look at what the term “software supply chain security” means, why it’s essential, and how you can help secure the supply chain for your project.
What is Software Supply Chain Security?
The software supply chain resembles other activities or industries in many ways. First, some resources are consumed, then transformed through steps and processes before being supplied to a customer as a service or product.
These steps and processes must run smoothly; therefore, we recommend you check out this article to learn more about how you can make sure your company runs smoothly.

Organizations can use software supply chain security to detect, identify, analyze, and mitigate risks associated with digital artifacts that enter their software via third parties such as open-source libraries, commercial software vendors, or outsourced development.
Moreover, in a comprehensive supply chain security plan, risk management and cybersecurity principles are merged to identify supply chain risks and apply methods to block, mitigate, or remediate them.

Software supply chain attacks happen by introducing malicious software into the supply chain. So, a supply chain attack is a threat actor’s attempt to compromise one or more organizations’ software and cloud environments.
Attackers could take advantage of commercial trust between software vendors and their customers or implicit trust between developer communities.
Benefits of Using Software Supply Chain Security?
Due to supply chain attacks becoming more common in recent years, the focus on software development has intensified. The Executive Order on Improving the Nation’s Cybersecurity recently outlined best practices for supply chain security for businesses.
It aims to address supply chain compromises in which hackers gain access to the development process and inject malware into the source code.

This malware was able to spread downstream in published software, allowing attackers to steal data from the companies using it. Furthermore, the Executive Order encourages US companies to develop more secure software supply chains and avoid compromises that could disrupt critical infrastructure functions.
Securing the Application Source Code
The code you write is the part of the supply chain you have the most control over during the software development lifecycle. Therefore, it makes no difference if a secure supply chain is shipping insecure code.
However, you can help mitigate supply chain attacks by implementing strategies to ensure this code is safe.

With VMware Tanzu, you’ll improve automated tooling and DevSecOps practices to securely ship high-quality code to production while also fixing security vulnerabilities faster. Create ideas on a safe platform and utilize DevSecOps techniques to deploy code quickly and with less friction.
JFrog, a security and compliance solution, is another supply chain security option. It enables you to deliver trusted software, innovate at speed and scale, and simplify compliance with security regulations, standards, and internal policies.
App Dependency Management
Few developers create their builds from the ground up. Instead, they use prebuilt code from open source and other catalogs to save time and speed up development, especially when it comes to blockchains, where vulnerabilities have increased many folds.
Therefore, when checking for and patching vulnerabilities in the app in production, software must consider the pieces of prebuilt code integrated into the final build.
Your teams must be able to visualize their application dependencies to ensure secure software design and development. Regular scanning ensures that all dependent libraries are patched and free of Common Vulnerabilities and Exposures (CVEs), reducing the likelihood of a dependency being exploited.
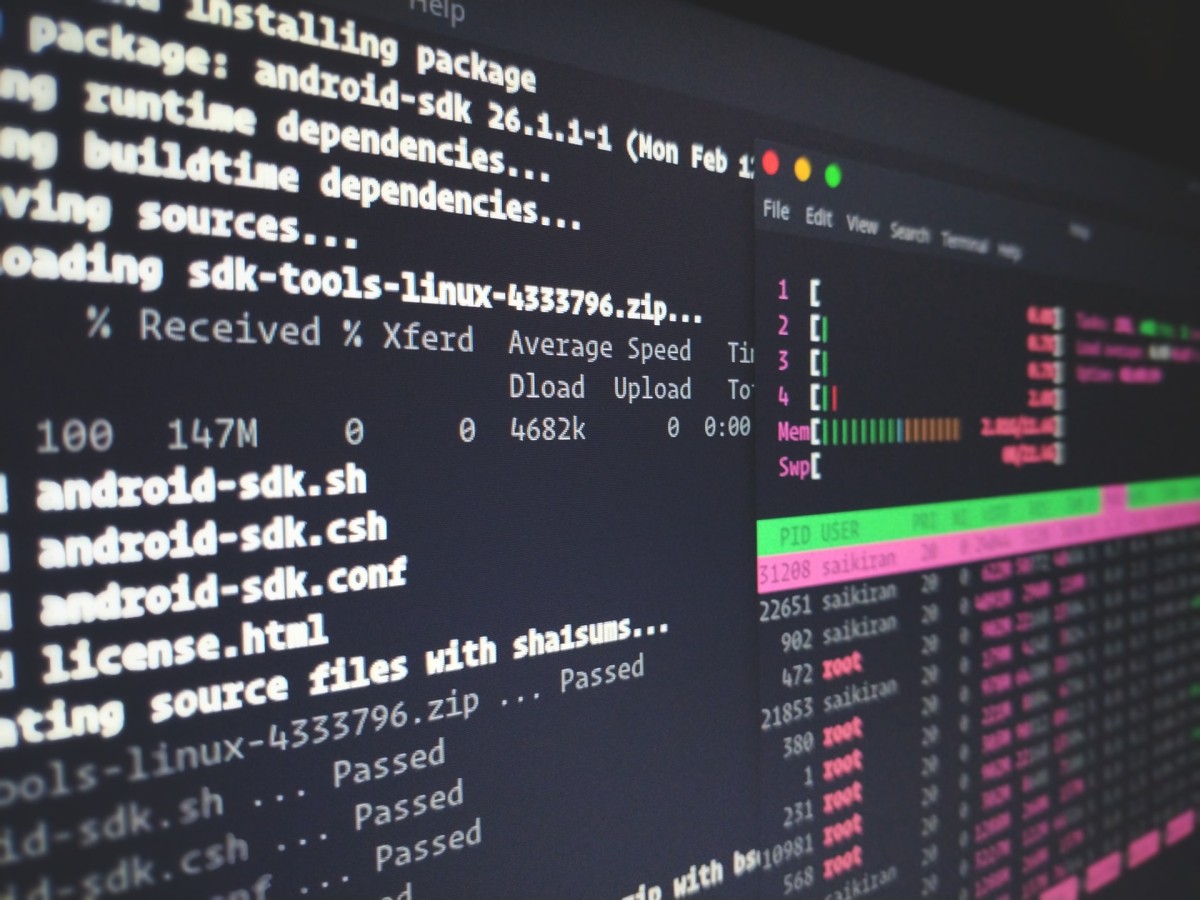
Secure CI/CD Systems
Good governance requires good governance to control your continuous integration and delivery (CI/CD) pipeline. For example, ensuring that system permissions are configured correctly to help secure your software supply chain.
This includes the bare minimum of privileges.
Secure Image Build and Registry
When it comes to making container images more secure, the goal is to reduce the number of high-risk CVEs in the image registry, and the time it takes to fix CVEs. This can be accomplished by ensuring that base images are trusted and signed as well as enforcing image repository control policies.
Final Thoughts
Security activities are required throughout the DevOps process to reduce the risk of software supply chain attacks. While there is still a lot of manual work to be done today, software supply chain tools are improving as the DevSecOps industry becomes more aware.
Understanding and mitigating vulnerabilities along the path to production reduces the risk of business investments, allows for faster delivery of more secure software to end-users, and reduces friction for developers deploying code.
JFrog offers solutions for secure tooling with operator-defined guardrails that developers will love to use.



